Network Call Record Verification Set – erl0001900, 103.194.170.154, 111.190.150.204, 111.90.150.20r, 1mfrrefsntb470ctl009, 5xtxux7, 720PNQ, 81jkz9189zkja102k, Aktnafq, Aliunfobia
The Network Call Record Verification Set erl0001900 offers a structured lens for assessing recorded traffic, focusing on data integrity, provenance, and reproducibility. Key IPs and identifiers are cross-referenced to test authenticity and traceability within a controlled workflow. The approach emphasizes anomaly detection, attribution, and lifecycle monitoring as core components. This frame raises questions about how signals align with real-world events and where gaps may emerge, inviting further scrutiny into verification mechanisms and their practical limits.
What Is the Network Call Record Verification Set erl0001900?
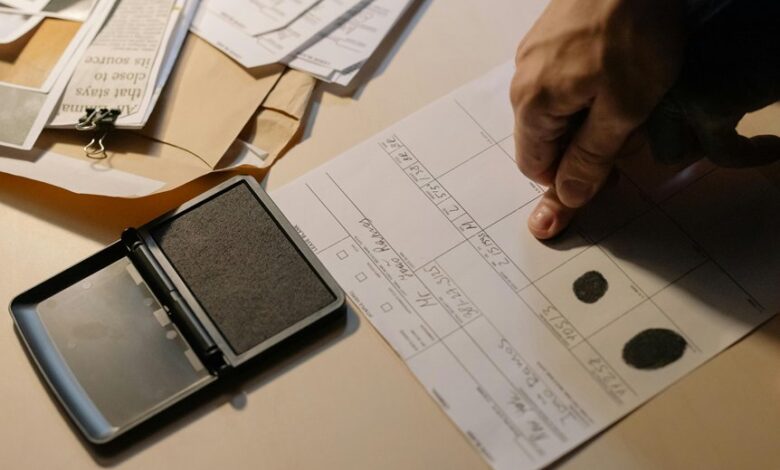
The Network Call Record Verification Set (NCRVS) erl0001900 is a defined collection of criteria and procedures used to assess the accuracy and integrity of recorded network call data.
It implements rigorous network verification and data integrity checks, documenting sample scope, timing, and cross-reference rules.
The approach is analytical, methodical, and focused on reproducible evaluation without extraneous interpretation or ambiguity.
How Do IPs and Identifiers Validate Call Authenticity?
How do IPs and identifiers contribute to validating call authenticity within the Network Call Record Verification Set? IPs and identifiers provide traceable origin signals and contextual metadata that analysts cross-verify against expected patterns. This discipline ensures call authenticity by detecting spoofing, mismatches, or irregular routing, enabling precise attribution, auditability, and confidence in recorded interactions without speculative inference.
Practical Steps to Detect Anomalies Using erl0001900 Data
Practical steps to detect anomalies using erl0001900 data require a structured, data-driven approach that prioritizes traceability and repeatability. Analysts implement baseline models, monitor outliers, and validate identifiers through cross-checks with known patterns. The process emphasizes anomaly detection techniques, timestamp consistency, and sequence integrity, while identifier validation ensures correct source attribution and reduces false positives in routine network call analyses. Proceed methodically.
Implementing Security Monitoring and Lifecycle for Modern Networks
Security monitoring for modern networks requires a structured lifecycle that integrates continuous visibility, rapid detection, and disciplined response processes. The discussion examines governance, data provenance, and instrumentation, enabling consistent security monitoring across heterogeneous environments. Lifecycle management emphasizes measurable milestones, automated validation, and adaptive controls. By formalizing roles, metrics, and feedback loops, organizations sustain resilience while preserving freedom to innovate within secure boundaries.
Conclusion
The conclusion juxtaposes precision with fragility: the erl0001900 framework anchors verification in exact IPs and IDs, yet real-world networks remain fluid and noisy. Methodical cross-checks—timestamp alignment, provenance cues, and anomaly scores—provide a sturdy backbone, while divergent signals invite scrutiny. In this tension between reproducible rigor and evolving threat landscapes, disciplined workflows ensure reproducibility even as adaptive adversaries exploit subtle discrepancies. Ultimately, structured verification sustains confidence without neglecting the gaps that demand vigilance.




