homedecorchamp
-

Advanced Monitoring Classification Index – 18552195933, 18552225919, 18552555458, 18552562350, 18552793206, 18553414643, 18554202327, 18554309246, 18555601400, 18555645748
The Advanced Monitoring Classification Index (AMCI) consolidates ten identifiers to normalize roles, metrics, and domain use across monitoring ecosystems. This standardization supports cross-domain routing, provenance tracing, and consistent anomaly assessment. By aligning signals with thresholds and governance practices, AMCI offers scalable governance and predictive resilience. The framework invites scrutiny of implementation strategies and real-world impact, but its true value will…
Read More » -
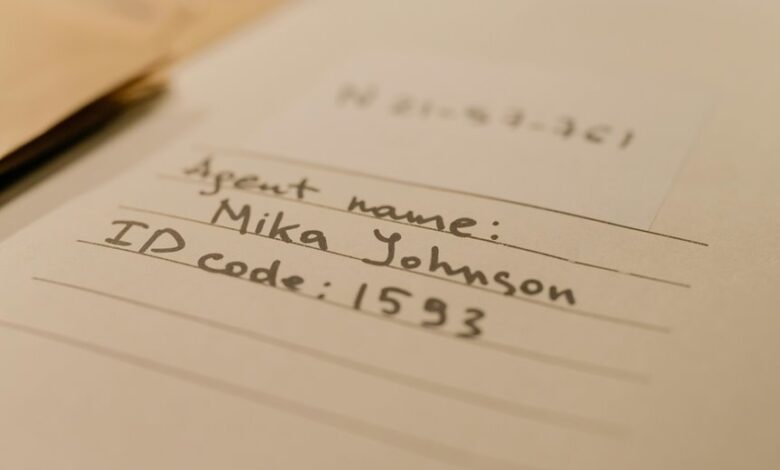
Operational Security Examination File – 18445424813, 18446631309, 18447300799, 18447312026, 18447410373, 18447560789, 18448982116, 18449270314, 18552099549, 18552121745
The Operational Security Examination File series presents ten structured dossiers, each detailing aims, methods, and findings across multiple case scenarios. The framework supports cross-environment auditing, with identified gaps, controls, and resilience factors mapped to actionable measures. Findings are translated into incident playbooks and risk-based alerts, designed for traceability and continuous improvement. The compilation emphasizes lawful data handling and governance, ensuring…
Read More » -

Cyber Intelligence Review Matrix – 18339421911, 18339726410, 18339793337, 18442087655, 18442550820, 18443876564, 18443963233, 18444727010, 18444964650, 18444964651
The Cyber Intelligence Review Matrix consolidates ten threat identifiers into a unified framework for prioritization and response. It translates complex threat intel into measurable indicators, supporting repeatable playbooks and transparent governance. Each identifier links to actors, tactics, and risks, enabling evidence-based decisions and traceable incident handling. The approach promises faster decisions and consistent measures, but its practical value hinges on…
Read More » -

Enterprise Validation Tracking Sequence – 18009016182, 18009320783, 18009372000, 18009473131, 18009730600, 18332147629, 18333110849, 18333560681, 18335421564, 18336972406
The Enterprise Validation Tracking Sequence names a structured governance framework that translates strategy into concrete checks across complex systems. Each identifier signals a stage in a repeatable validation flow, with clear accountability and auditable outcomes. The sequence emphasizes risk prioritization, resource alignment, and transparent decision points. Its deterministic paths enable corrective loops and scalable assurance across interfaces and compliance requirements.…
Read More » -

Secure Connectivity Observation Archive – 18006727399, 18006783228, 18007727153, 18007784211, 18007822200, 18008154051, 18008290994, 18008503662, 18008609072, 18008887243
The Secure Connectivity Observation Archive consolidates signals from 10 identifiers into a privacy-preserving, governance-driven repository. It emphasizes secure aggregation, provenance-traceable data, and standardized signals while enforcing cryptographic protections and access controls. The framework supports auditable pipelines and scalable interoperability for operators and policymakers. As the archive evolves, questions arise about how safeguards balance transparency with privacy and how governance will…
Read More » -

Digital Infrastructure Reliability Ledger – 18005588472, 18005614248, 18005672639, 18005694879, 18005886718, 18006564049, 18006657700, 18006674720, 18006688850, 18006708411
The Digital Infrastructure Reliability Ledger (DIRL) consolidates performance, reliability, and governance data for critical digital systems, enabling standardized telemetry and auditable reporting. It ties interoperability standards to concrete metrics, supporting proactive incident response and automation governance. Case studies illustrate cross-domain interfaces, data schemas, and risk benchmarks. With real-time telemetry and transparent SLAs, DIRL promises measurable uptime gains while defending privacy…
Read More » -

Worldwide Identity Authentication Register – 18004224234, 18004474791, 18004590911, 18004636236, 18004637282, 18004637843, 18004653863, 18005040716, 18005311925, 18005495967
The Worldwide Identity Authentication Register consolidates cross-border verification standards, governance, and data-sharing practices to support legitimate access to services. It links a set of identifiers to interoperable workflows, auditable decisions, and scalable integration, all under privacy-by-design and risk-based governance. The framework aims for transparency and accountability while reducing jurisdictional redundancy. It raises questions about governance, compliance, and future-proofing that merit…
Read More » -

Final Consolidated Infrastructure Audit Report – 18002904014, 18003144944, 18003558123, 18003594107, 18003613223, 18003613311, 18003646331, 18003680038, 18003751126
The Final Consolidated Infrastructure Audit Report aggregates domain-specific findings across nine audit identifiers, presenting a disciplined assessment of exposure, controls, and governance. It identifies material risks, aligns remediation with owners and timelines, and emphasizes independent verification, dual controls, and periodic attestations. The document outlines actionable mitigations, a prioritization-driven roadmap, and opportunities for cost optimization. It sets a clear context for…
Read More » -

Next Generation Record Validation Chain – 16193590489, 18002251115, 18002485174, 18002623246, 18002631616, 18002631810, 18002675199, 18002752036, 18002762317, 18002886661
The Next Generation Record Validation Chain integrates multiple nodes—16193590489, 18002251115, 18002485174, 18002623246, 18002631616, 18002631810, 18002675199, 18002752036, 18002762317, and 18002886661—into a cohesive provenance framework. It emphasizes layered validation, tamper-evident proofs, and modular checks to sustain data integrity and traceability. The architecture prioritizes interoperability and governance transparency, with privacy preservation and ongoing monitoring guiding operations. The next questions concern how these elements…
Read More » -
Operational Data Tracking Archive – 9727530822, 9727643613, 9727988639, 9735219699, 9738434455, 9738697101, 9738810100, 9803437450, 9844803533, 9898634633
The Operational Data Tracking Archive consolidates performance metrics, events, and decisions into a standardized ten-digit schema for deterministic access. It supports governance, traceability, and institutional memory while enforcing data quality and security controls. By unifying diverse data streams, the archive enables consistent lineage and auditable workflows. The framework invites scrutiny of governance practices and archival methods, inviting further examination of…
Read More »
