Verify Call Record Entries – 7572189175, 3715143986, 081.63.253.200, 097.119.66.88, 10.10.70.122.5589, 10.24.0.1.71, 10.24.1.533, 10.24.1.71/gating, 111.150.90.2004, 111.90.150.1888
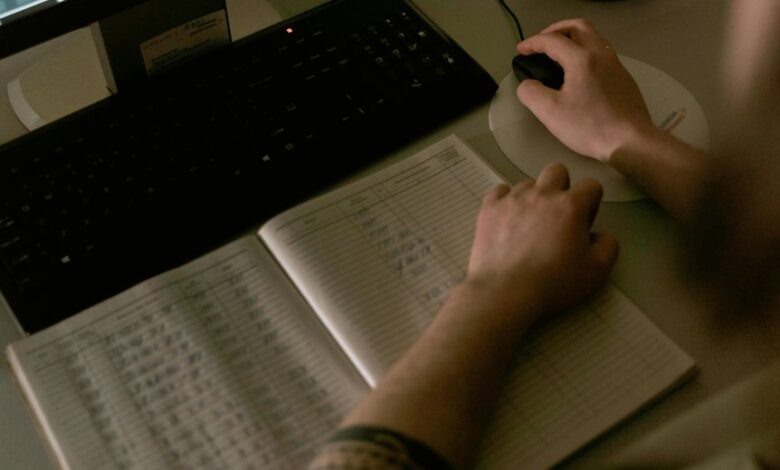
A disciplined approach to verify call record entries must start with exact-field alignment: IDs, timestamps, durations, outcomes, and provenance must map to a unique, non-colliding core set. Anomalies like malformed tokens (111.150.90.2004) or gateway suffixes (10.24.1.71/gating) require flags and rationale. The framework should enforce monotonic sequences, cross-field consistency, and auditable origin for each item, from 7572189175 to 111.90.150.1888. The challenge lies in assembling these signals into a deterministic checklist that surfaces inconsistencies without ambiguity, prompting further investigation.
What These Call Log Entries Are Trying to Tell Us
Call log entries encode a structured record of telephone activity, each field—time, duration, caller ID, and outcome—contributing to a composite picture of communication patterns. The data invites interpretation without presuming motive; patterns emerge from consistent timing, recurring IDs, and cross-network routing. However, irrelevant speculation and unrelated assumptions must be avoided to preserve analytic integrity and freedom through disciplined evaluation.
Build a Validation Framework for Timestamps and IDs
A validation framework for timestamps and IDs centers on establishing strict, verifiable criteria that distinguish accurate records from artifacts.
The approach emphasizes repeatable checks, deterministic rules, and auditable provenance.
Timestamp validation enforces format, range, and monotonicity, while ID verification confirms uniqueness, structure, and collision resistance.
This framework enables reliable data parity, governance, and scalable, frictionless integration for users seeking freedom.
Decode Nonstandard Formats and Flag Anomalies
Decoding nonstandard formats and flagging anomalies requires a disciplined, rule-driven approach that distinguishes legitimate irregularities from systemic errors.
The evaluation concentrates on pattern deviations, encoding quirks, and cross-field consistency.
Analysts verify anomalies by isolating outliers, normalizing irregular tokens, and applying timestamp validation to confirm sequence integrity, while preserving audit trails.
Clear criteria ensure robust, scalable detection without overfitting.
Put It All Together: A Practical Verification Checklist
In practical verification, a structured checklist synthesizes insights from prior analyses—ensuring that decoded formats, anomaly flags, and cross-field validations cohere into a repeatable workflow. The verification framework guides stepwise validation, enabling consistent documentation and auditability. Anomaly detection integrates thresholds, correlation, and baselined expectations, while independent checks confirm data integrity, timeliness, and source credibility for robust, freedom-oriented verification outcomes.
Conclusion
In sum, the verification process is a precise lattice of checks: exact field matches, unique IDs, and monotonic sequencing guard against drift; IP-like tokens and domain patterns are validated, while malformed tokens (e.g., 111.150.90.2004) and gateway suffixes (10.24.1.71/gating) are flagged for anomalies. The framework assembles cross-field consistency with auditable provenance, ensuring every entry—such as 7572189175 or 111.90.150.1888—persists with deterministic integrity, like a meticulously mapped tectonic grid powering a faultless data harbor.




